IDScout
Project Overview
IDScout is a mobile app that aims to provide users a simple and efficient way to investigate and monitor their online identities. This is a class project from the department of Human-Centered Design and Engineering (HCDE) at the University of Washington, Seattle.
My Role: UX Researcher
Conducted literature review, survey, and interviews to drive product directions and defined key features.
Led and analyzed usability testing to validate the product direction and drove design changes with cross-functional teammates
Teammates
1 PM/Researcher, 2 Designers
Duration
~2 months
Background
With an increase in data breach incidents, we wanted to understand people’s experiences with data breaches and online identity protection. Without much knowledge in the space, we conducted exploratory research to learn about the space of data breaching and looked for opportunities.
Research Questions
“How might we improve the process of learning about, monitoring, and acting upon data breaches for internet users in the United States?”
How do users want to discover/be informed that their data has been breached?
What information do users want to know about an incident?
What next steps/resources would users want to take after being informed of a data breach?
How can we provide users with trust in our service?
Do users want to learn long-term data privacy practices?
Project Timeline
Research
Literature Review
We conducted a literature review because it helps the team to gather a wide range of insights on the topic, the potential target users, and the inclination of their needs. We looked for general information about internet users’ attitudes towards privacy, their expectations, and concerns regarding data protection, and the current environment of internet security.
Findings
Target user age group
People under 45 are most concerned about information privacy and are more likely to become knowledgeable about data protection(Cisco, 2019).
Lack of proactivity
Most users are concerned about data breach incidents, but few take the actions to prevent (or mitigate) them.
Problem magnitude
People under 45 are most concerned about information privacy and are more likely to become knowledgeable about data protection(Cisco, 2019). 2020, data breaches are increasing at an alarming rate of 273% increase over 2019(Identity Force, 2020).
Lack of trusting solution
Trustworthiness is the top concern for users when it comes to engaging with an aggregator of breaches "hacked or not” type of service for data security monitoring
Survey
The literature review gave us good understandings of the problem space, our potential target users, and opportunities. Armed with an understanding of our target users, I decided to distribute a user survey to better understand how people become aware of data breaches.
Recruitment
We distributed a survey through the UW student groups and personal networks. The survey included questions asking people’s demographic information, people’s experiences with data incidents, what people want to know when breaches happened, and how did they react to them.
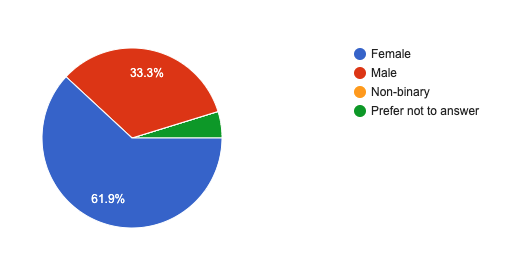
Note: Most participants identified as female
Note: All participants were target audience between 18-45
Findings
Confusion
Participants were confused about what type of personal data was affected in data breach incidents and how much of their personal data were affected
Data breach occurrences
The majority of participants have experienced at least one data breach incident
Lack of direction
Participants who believe they have not experienced a data breach do not aware of steps they can take to protect their personal data. Participants who have experienced data breach change passwords or utilized other credit services to detect account anomalies
Interviews
I decided to conduct structured interviews to understand the mental-decision making process of our participants regarding data breaches and bring clarity to our design solution. We prepared a set of questions that focused on user’s past experiences when dealing with data breaches to look for pain points.
Findings
Too many information
Participants were frustrated about sorting through emails and desired centralization of all information. Those who waited longer between breach and time of notification were less satisfied with the alert process.
Lack direction
It was hard to validate information and participants
Dissatisfied with password resetting
Resetting (similar) passwords from other accounts are tedious
“Sometimes I ended up forgetting the password to some websites, and that frustrated me ”
Personas
Based on the literature review, user survey, and in-depth interviews, we listed user’s needs and pain points to create personas, we were able to apply them into our design solutions.
Sketch & Ideation
With research insights and persona’s in mind, we created a set of solutions individually and came together to decide our top choices. We did not limit ourselves to only digital solutions, we also created physical solutions for the product.
Initial Solutions
A password keeper that saves all user’s passwords and allows easy updates. This approach removes the tedious process of having to update passwords one by one. Users can choose to update their passwords automatically or manually.
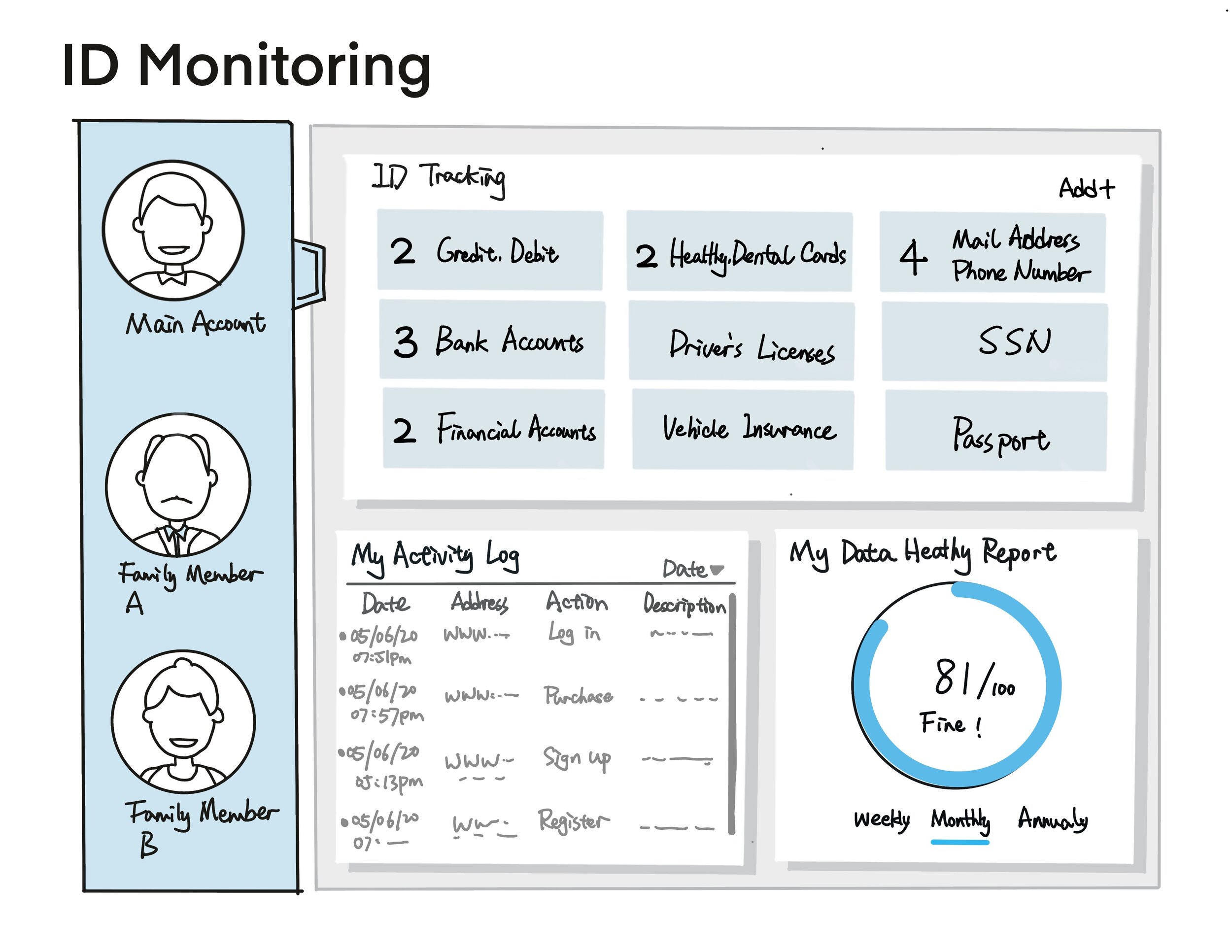
A data monitoring center that allows users to monitor all types of personal data and gives users the ability to customized the system to their preference. This approach centralized all information so users do not need to go through different sources to find what they need.
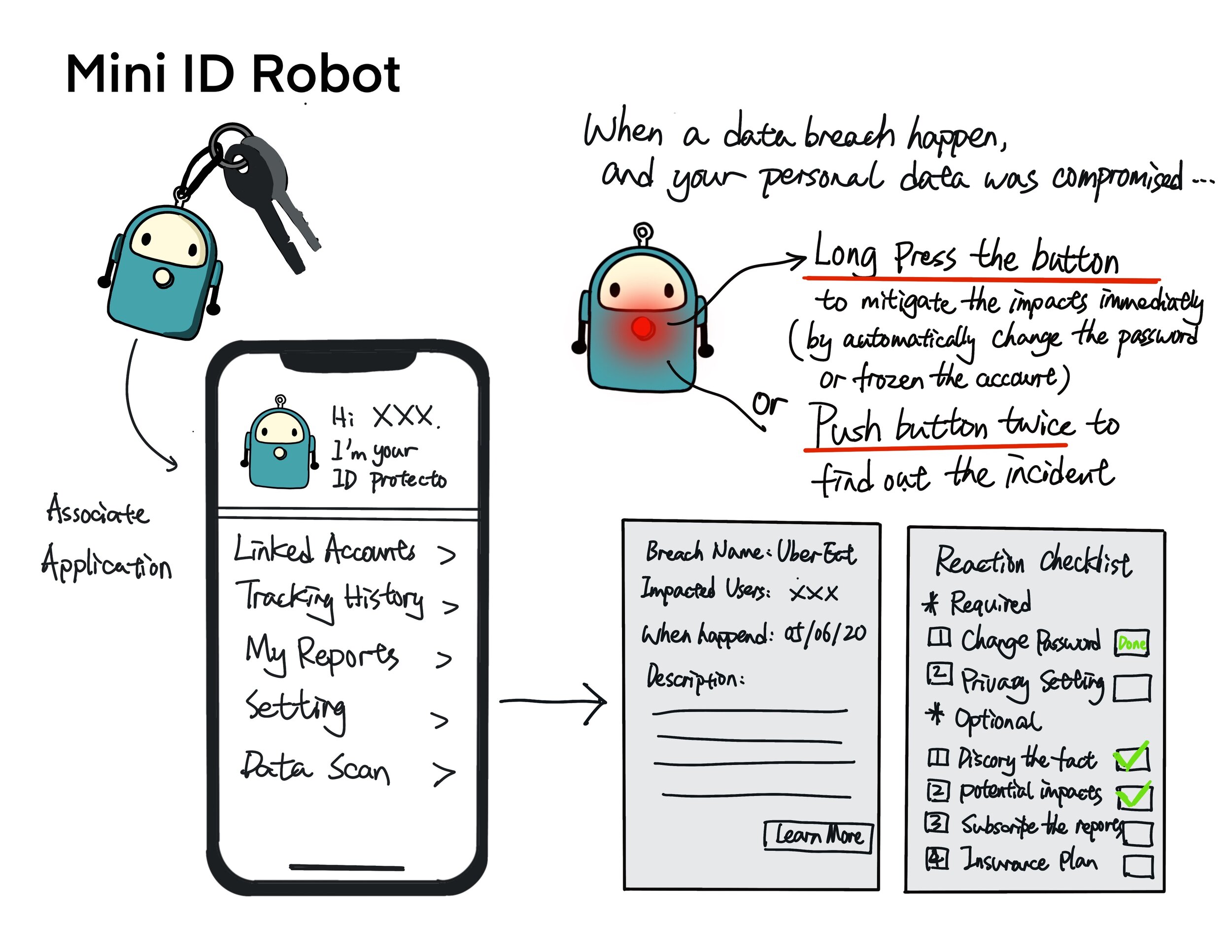
A keychain alert that allows the users to get the data-related notification in a timely manner and the product allows customization for “short-cut” actions. (we discarded this solution based on user research and replace it with a digital notification center)

Storyboard
We created a scenario storyboard to better understand the design and flow of our solution, the storyboard walked through the process of setting up an application, updating passwords, and monitoring online personal data.
Prototypes
Usability Testings
Based on the ideation and sketch, our team created a mid-fidelity prototype. We decided to conduct usability testings to learn if the participants can complete the task we provided, and what confusion and pain points participants encountered.
We recruited 5 participants total for the usability testings. We set up 6 tasks based on the app features: onboarding, the home page, data monitoring, account page, password update, and settings. We asked participants to complete each task using think-aloud methods and asked them about their experiences throughout the process.
I analyzed the usability data using a Google spreadsheet, the findings help us to make design changes and we handed in a high fidelity prototype as our deliverable.
Takeaways & Reflections
Aligning design and research timeline is key to meet deadlines
Manage research priorities and inform teammates at all times
If given more time, I want to interview industry experts to understand the space and conduct a competitive analysis on similar products